Blog
Cloud Migration Considerations
With companies seeking the best return on investment for their technology expenditure, Cloud migration, or, in some cases, migrating to a different Cloud environment or changing to a new Cloud provider, can be a good choice. Read on to learn more about the benefits of using the cloud as well as what to consider before migrating.

Everything You Need to Know About Multi-Factor Authentication
Imagine if no matter how well protected your computer systems are, there was yet another level of protection? One which involves specific factors particular to the user, which they can use in addition to a strong password? With multi-factor authentication (MFA), you have yet another defense against bad actors seeking to infiltrate your network. Read on to learn more about this relatively new technology.

October is Cybersecurity Awareness Month: Be Aware and Prepared
October is National Cybersecurity Awareness month, a “collaborative effort between government and industry to raise awareness about the importance of cybersecurity, and to ensure all businesses have the resources to be safer and more secure online.” This year, according to the US Department of Homeland Security, the emphasis is on a proactive approach. Read on to learn more about various aspects of cybersecurity.

Protect Your Business Through Cybersecurity Awareness
October is Cybersecurity Awareness month and knowing this can serve as a wake-up call to protect your company’s data, networks and systems from internal and external hazards. Read on to learn more about protecting your business.

The Importance of Data Protection Before a Disaster
Hurricane Dorian is just one event that can potentially affect a business’s access to its data and reemphasizes the importance of having a data protection plan in place. Other events can have the same effect—cyclones, earthquakes, and hurricanes–suspending business operations for days or weeks. Even a brief power outage can put your company at risk, not to mention the threat of cyberattacks. Read on to learn more about keeping your business’ data safe and accessible.

Monitor Your Network to Keep it Safe and Thriving
With technology ever changing and progressing, more is demanded from your network than ever before. Cloud computing, along with multiple applications and huge amounts of data, demand a strong and healthy network. Read on to learn more about how to monitor your network and maximize its flexibility, efficiency and security.
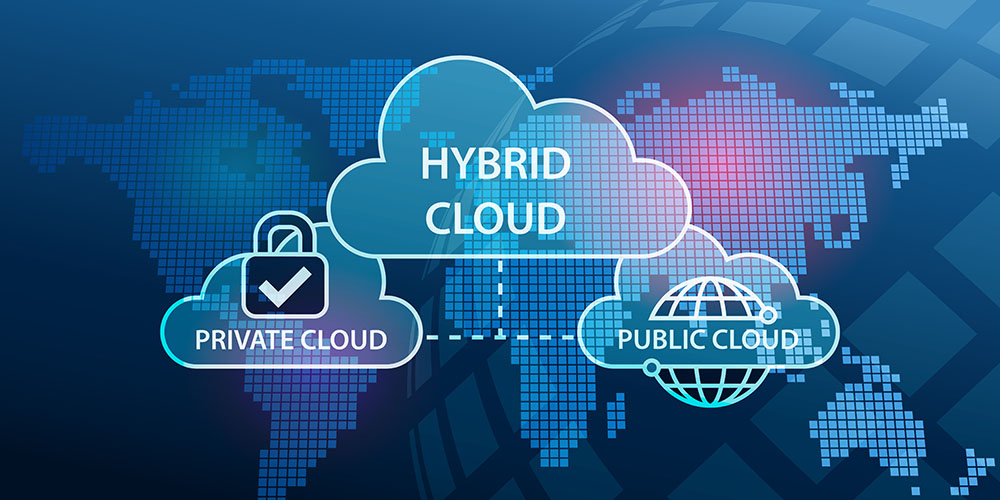
Hybrid Cloud Considerations
Cloud computing, despite varying levels of adoption, has become a common way for a business to avail itself of computing resources without having to maintain expensive infrastructure. Companies can use varying levels of resources, scaling up and down as demand and usage changes.

Train Your People to Fight Cyberattacks
With the advance of technology, many benefits have come to businesses—commerce taking place twenty-four hours a day and the ability to have meetings with workers half a world away, among others—but cybercriminals have learned to exploit technology, using practices such as phishing (planting a fraudulent link in an email) to gain access to business’s data and networks.

The Importance of Data Protection in Business Continuity and Disaster Recovery
In the last week, two earthquakes have shaken southern California, alerting us to the need to have our businesses prepared for a disaster, whether natural or manmade. Not only can fires, floods and earthquakes cause business interruptions, but so can systems failures, human error, malware and ransomware attacks.

Consider Unified Communications for Your Business
Imagine being able to integrate business class phone systems, collaboration and virtual meetings and your contact call center all within a secure and reliable unified communications suite. This means you can work anywhere, get customer information instantly and route calls efficiently to communicate in real time all over the world. Increasingly, Unified Communications can integrate your office communications and help you help customers.
